The security boundaries for enterprises employing public cloud resources are blurring in today’s world of hybrid cloud infrastructures that use both on-premise and public cloud Infrastructure-as-a-Service (IaaS) or Software-as-a-Service (SaaS).
Many businesses are turning to cloud security technology. It is well-known as a reliable data storage alternative, and it’s swiftly gaining popularity due to its more flexible security system management, ease of use, and interoperability thanks to open API architecture.
Cloud-based security technique offers great ability to integrate any system, even seemingly disconnected ones, allowing for remarkable expansion and scalability. Security technology becomes more holistic and manageable as a result of open APIs, simplifying management.
What are Open-APIs?
An open API, often known as a public API, is a software developer-accessible application programming interface. Open APIs for developers are publicly available on the internet and can be freely shared, allowing the owner of a network-accessible business to provide consumers with universal access. You can use open APIs to gain access to existing software programs and write code to make communication between different technologies faster and easier. They serve as the foundation for the code, making the development process easier and faster.
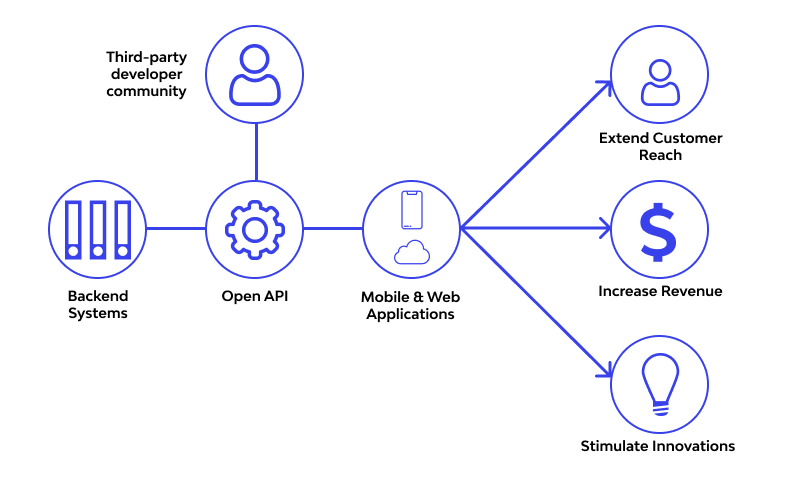
How are Open-APIs Securing Cloud Services?
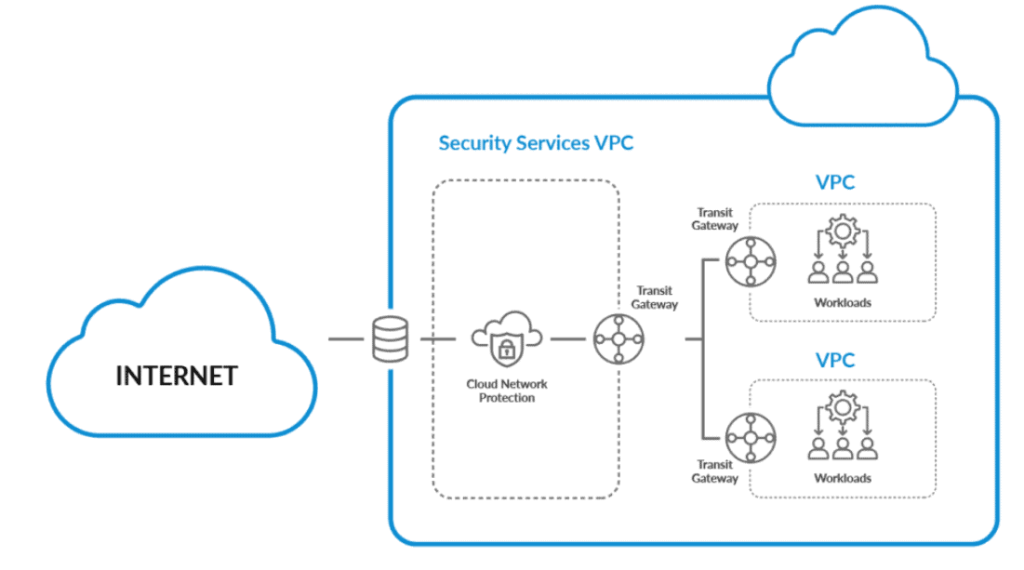
The future of security is open APIs because they enable cloud security architecture to cooperate and reach its full potential. Open APIs enable security systems from many vendors to exchange data with one another, enriching their existing data. They aid in facilitating and improving security management to safeguard your company.
To link your IoT devices and enable data transmission between them, you can use open APIs. There are new chances to improve workflow and improve the overall security posture of your system by getting data from another device.
IoT devices may use data to make smarter decisions more quickly, improving the accuracy and productivity of security system workflows. No system needs to remain separate any more thanks to cloud-based technology. Systems that were once seen as different can cooperate and communicate efficiently to improve their security.
Building management and physical access are an illustration of two systems that have never before been integrated properly. Your access control system may communicate when to turn on the lights or adjust the temperature based on usage and entrance activities if it is integrated with lighting and HVAC technologies.
This is a good substitute for motion sensors, which not only come at a higher cost and require more installation work but also necessitate constant movement inside an office or conference room to prevent the lights from going out.
This level of flexibility was previously only possible with managed, on-premises systems, and then only with the help of an on-site, specialized IT, specialist. To give on-prem security technology more flexibility and control, several on-site solutions now include browser-based control.
Security teams can monitor real-time activity logs and video streams and receive notifications of potential problems via mobile devices when using an integrated cloud-based access control system. Security management with open APIs will be simpler and more effective without sacrificing quality thanks to the ability to start site lockdowns, broadcast live video to first responders, or remotely modify access rights.